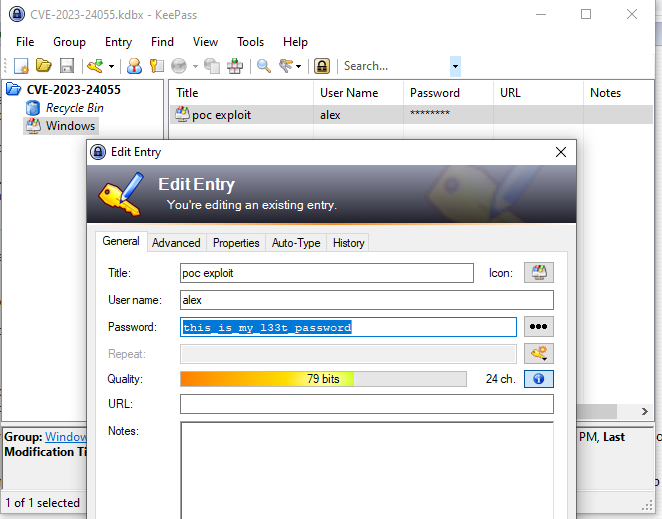
The new version of the password manager KeePass 2.53.1 addresses a potential security flaw (CVE-2023-24055).
Last week, a report regarding a security vulnerability in KeePass with the identifier CVE-2023-24055 appeared on the Internet. The problem, according to Belgium’s Federal Cybersecurity Emergency Response Team, was the apps’ trigger mechanism.
If it has a trigger, an attacker can export the full password database to a second. The primary issue is that KeePass did not request the user to enter a master password before exporting passwords.
The KeePass team attempted to convince it that a key was the system’s lullaby. Such an assault would simply limit the attacker’s ability to write to the system, so malicious acts such as reopening the executable and launching malware and modifying the system’s autostart and configurations would still be possible.
The chief developer of KeePass, Dominik Reichl, advised users to create a forced configuration file to enable the trigger function. An attacker with write access can modify the configuration file so that the fundamental problem is not resolved.
Such an attack can be fully averted if the users are vigilant and the system is secured by a current antivirus and firewall.
The KeePass user had multiple alternatives for problem resolution. It was feasible to switch to an older version of the password manager KeePass 1.x that is still actively supported. Some features, such as the trigger-patch, do not exist. In addition, we intended to switch to ported versions of KeePass. This method has the advantage of being able to generate files using password data.
The issue was resolved with the KeePass 2.53.1 upgrade. According to the official release notice, the Export Don’t Ask for Key option has been removed, and KeePass now always requests the current master key when exporting data.
In other words, KeePass will always prompt the user to confirm that he has the necessary data before executing a command. Before initiating the data export, you can check the process with the master password.
This blemish is likely a result of the heated talks and fierce disagreement. Reichl may not have changed his position that there was no vulnerability in effect, but he modified the app in response to public concerns so he could have claimed so.
The most plausible explanation is that few KeePass users utilise this function. Password export triggers are utilised relative to other users.
Users of KeePass are encouraged to upgrade to version 2.53.1 in order to avoid their passwords from being exported automatically. Check your KeePass security settings to ensure that your database is adequately protected from brute-force assaults.
Related Articles:
Ways Parents Can Help Their Children Break Free From Technology Addiction
Google, Microsoft and 15 other technology companies headed by Indian-origin executives
Fans of The Last of Us Are Emotional Wrecks Following the Conclusion of Episode 5: “My Heart Hurts.”